Cisco OT security and networking architecture named in 2024 IoT Breakthrough Awards.
First published by Cisco.com - January 11, 2024
With a unified industrial security and networking architecture, Cisco brings simplicity and scale to both connect and protect operations. It reduces complexity by delivering visibility, segmentation, remote access, and other security services on Cisco industrial switches and routers without the need to introduce additional hardware.
- Visibility into connected assets, network traffic, and assessing existing asset vulnerabilities is recognised as the first step in securing operations. Traditional security vendors provide a deep packet inspection (DPI) server for this purpose to which you need to span traffic from your switch ports, adding to the network complexity and costs. Cisco Cyber Vision runs within Cisco industrial devices and performs the same functions without the extra server, complications, and expense.
- The second step once visibility is established is to partition your industrial network into smaller segments to contain any malware that may find its way inside, but in a way that allows legitimate traffic to flow unhindered. Traditionally, this network segmentation has been done with sets of firewalls or Access Control Lists (ACL) configuration in switches. Both are either expensive, difficult to get right and maintain, or both. Native capabilities in Cisco Industrial Ethernet Switches allow dynamic and automated multiple levels of segmentation without the firewalls or manual ACLs.
For more details see the whitepaper, Harness the Power of Networking to Secure Industrial Operations.
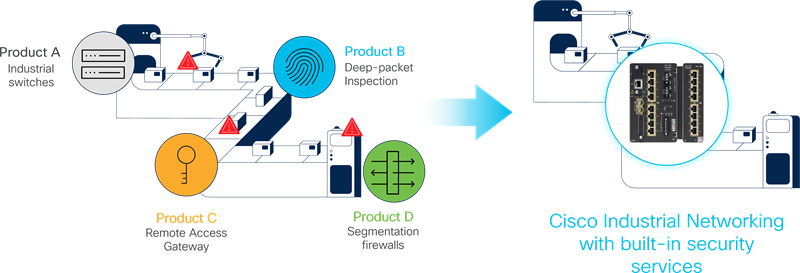
Figure 1: Cisco industrial switches and routers integrate security functions and help eliminate many separate products
Download Whitepaper
Harness the Power of Networking to Secure Industrial Operations
This white paper explains how modern industrial network equipment can embed a full range of advanced security applications to build a converged architecture that will bring simplicity, ease of deployment, and cost savings and help scale industrial security to protect operations.